ClamAV client/server setup
Note: This may very well be well-known information, but I found it difficult to get exact answers from the official ClamAV documentation, available man pages, and other kinds of documentation. The most useful hint originated from a mailing list thread considering ClamAV version 0.70, which is getting rather outdated.
My original issue was getting antivirus functionality with mod_security and Apache on a Raspberry Pi server. Due to memory constraints it seems Apache and ClamAV (my version at the time of writing: 0.99) do not coexist happily on the same RPi unit. The obvious solution: Run the ClamAV daemon on a separate device, and set up mod_security with client-side scanning.
The command-line client for antivirus scanning with the ClamAV daemon is named clamdscan. In older Debian releases like Squeeze and Wheezy, clamdscan is included in Debian’s clamav-daemon package, so the daemon will be installed even though you only need the client. This has been fixed in Debian Jessie and above, where clamdscan has become a separate package.
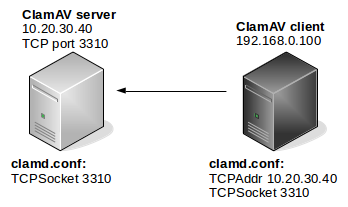
Both the ClamAV daemon (clamd) and the scanner client (clamdscan) have the same configuration file, unless otherwise specified. In Debian this is /etc/clamav/clamd.conf. Getting the client/server relationship configured is a matter of defining the socket on which they communicate. If the client and daemon (server) is running on the same system, the most efficient communication happens over a Unix socket (clamd.conf setting: LocalSocket). On different systems, however, you will need to use the settings TCPAddr and TCPSocket:
TCPAddr defines the IP address (and not TCP address, which would be a port number) on which the server should listen and/or which the client should make contact. Note that the documentation states that TCPAddr is used to define the IP address(es) clamd should listen on, and that it’s by default disabled. However, when setting TCPSocket and leaving TCPAddr unconfigured, clamd will listen on all IP addresses (0.0.0.0/:::). The documentation also makes no mention that the setting is used by clamdscan.
TCPSocket is the TCP port on which the communication takes place.
The following diagram illustrates the relationship:
Note: On a Squeeze/Wheezy Debian system, setting TCPAddr to a non-local IP address in clamd.conf will naturally make clamd (clamav-daemon) complain. You should disable clamav-daemon and clamav-freshclam on a client-only system:
# update-rc.d -f clamav-daemon remove update-rc.d: using dependency based boot sequencing # update-rc.d -f clamav-freshclam remove update-rc.d: using dependency based boot sequencing
After configuring as specified above, antivirus functionality should be tested with clamdscan. On the client node:
# clamdscan -v klez.exe klez.exe: W32.Elkern.C FOUND----------- SCAN SUMMARY ----------- Infected files: 1
On the server node, from the ClamAV log:
Sat Mar 5 20:31:59 2016 -> instream(local): W32.Elkern.C(16bc8fcec023b05b38af3580607bb728:92499) FOUND
Finally, I reconfigured the “runav.pl” file in mod_security by changing from clamscan to clamdscan.